Which two functions are provided by VMkernel ports? (Choose two.)
A. 802.1Q VLAN tagging
B. vSphere vMotion
C. ESXi Host Management
D. VXLAN Port Configuration
正解:B,C
質問 2:
What are the correct steps for connecting a virtual machine to a logical switch?
A. Select the vNIC, click the Add Virtual Machine Icon, select the logical switch.
B. Click the Add Virtual Machine icon, select the logical switch, vNIC to connect.
C. Select the logical switch, click the Add Virtual Machine Icon, select the VM, select the vNIC to connect.
D. Select the logical switch, select the virtual machine, click the Add Virtual Machine icon, select the vNIC to connect.
正解:C
質問 3:
If the Applied To scope is set to Distributed Firewall, which virtual machines will have the firewall rule applied?
A. All virtual machines on prepared hosts.
B. Only the virtual machines defined in the Source field.
C. All virtual machines in a Datacenter.
D. Only virtual machines defined in the Destination field.
正解:A
質問 4:
An administrator wants to perform Activity Monitoring on a large group of virtual machines in an NSX environment. How would this task be accomplished with minimal administrative effort?
A. Create a PowerCLI script to enable virtual machine data collection on each virtual machine.
B. Add the virtual machines to the pre-defined Activity Monitoring security group in Service Composer.
C. Create a security group in Service Composer and add the virtual machines to the security group.
D. Add the virtual machines to a VM folder in vCenter Server and enable data collection.
正解:B
質問 5:
An administrator needs to perform a configuration backup of NSX. From which two locations can this task be performed? (Choose two.)
A. Directly on the NSX Manager
B. Using the NSX API
C. Directly on each NSX Controller
D. From the vSphere Web Client
正解:A,B
質問 6:
In a Cross-vCenter implementation, where is the Universal Control Cluster deployed and configured?
A. In every vCenter instance associated with an NSX Manager.
B. In each vCenter instance associated with the Cross-vCenter implementation.
C. In each prepared NSX cluster associated with the Cross-vCenter implementation.
D. In the vCenter instance associated with the Primary NSX Manager.
正解:D
質問 7:
A network administrator is troubleshooting an issue and needs to observe an injected packet as it passes through the physical and logical network.
Which tool will accomplish this?
A. Activity Monitoring
B. Flow Monitoring
C. NetFlow
D. Traceflow
正解:D
質問 8:
An administrator is attempting to troubleshoot a routing issue between the Edge Services Gateway (ESG) and the Distributed Logical Router (DLR).
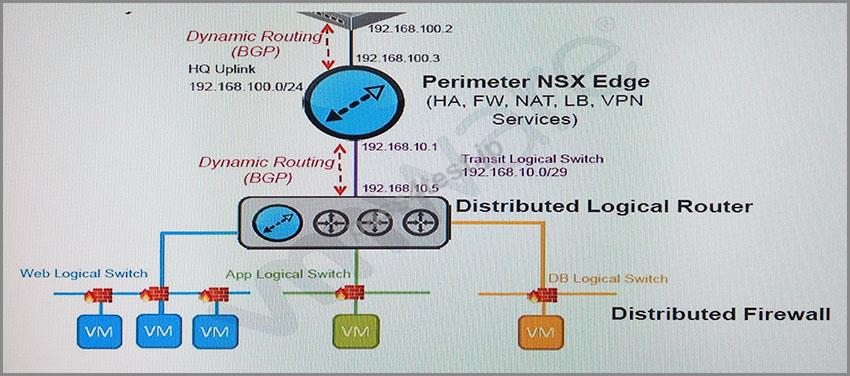
Based on the exhibit, which method CANNOT be used to troubleshoot the issue?
A. SSH session into 192.168.100.3 on the ESG.
B. Console session into the ESG.
C. SSH session into 192.168.10.5 on the DLR.
D. Console session into the DLR.
正解:C


 932 お客様のコメント
932 お客様のコメント クリック」
クリック」





Nakazawa -
2V0-642初心者から分かりやすく配慮した記述でコンパクトにまとめられていて、この一冊やり抜けば、余裕があれば別途問題集もやれば合格が視野に入ると思います。