You are setting up Junos Pulse client access to your Junos Pulse Access Control Service. Due to security policy, you need to ensure clients can only connect to the service when they are connected to the corporate network.
Which configuration steps meet the requirement?
A. Configure Junos Pulse Location Awareness with DHCP server and endpoint protection options.
B. Configure Junos Pulse Location Awareness with DNS server and endpoint address options.
C. Configure Junos Pulse agentless access with DNS server and endpoint address options.
D. Configure Junos Pulse agentless access with DHCP server and endpoint protection options.
正解:B
質問 2:
You want to allow users who authenticate to their Windows domain to authenticate automatically to the Junos Pulse Access Control Service.
Which two features should you configure on the Junos Pulse Access Control Service? (Choose two.)
A. Kerberos SSO
B. NTLMv2 SSO
C. Active Directory authentication server
D. LDAP authentication server
正解:A,C
質問 3:
What are two valid configurations for user-driven remediation when a Windows-based endpoint fails a Host Checker policy? (Choose two.)
A. Delete a file on the endpoint's file system.
B. Alter registry entries to prevent future execution of an executable, based on executable name and full path.
C. Download and run a remediation executable from the local software distribution server.
D. Kill a running process on the endpoint, based on executable name and MD5 checksum.
正解:A,D
質問 4:
On a MAG Series device, where is the preauthentication sign-in message configured?
A. On the sign-in page of the URL being used by the wireless users
B. On the sign-in policy of the URL being used by the wireless users
C. On the configuration page for the sign-in notification message
D. On the wireless user realm authentication policy
正解:B
質問 5:
You are attempting to create a Junos Pulse Access Control Service cluster. You select both the synchronize log messages and synchronize user sessions check (tick) boxes.
What information is replicated on the cluster nodes? (Choose three.)
A. log messages
B. ARP table
C. user records
D. SNMP traps
E. network settings
正解:A,C,E
質問 6:
Which three types of policies must you configure to allow remote users transparent access to protected resources using IF-MAP Federation between a Junos Pulse Secure Access Service and a Junos Pulse Access Control Service? (Choose three.)
A. Session-Export policies on the Junos Pulse Access Control Service
B. Session-Import policies on the Junos Pulse Secure Access Service
C. Session-Export policies on the Junos Pulse Secure Access Service
D. Resource access policies on the Junos Pulse Access Control Service
E. Session-Import policies on the Junos Pulse Access Control Service
正解:C,D,E
質問 7:
-- Exhibit -
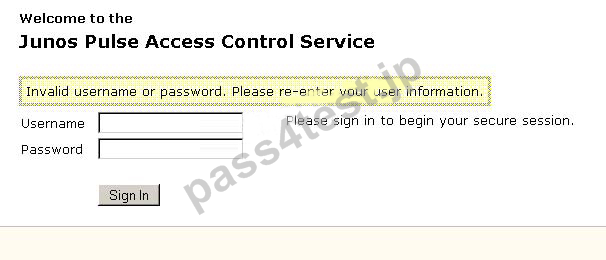
-- Exhibit -Click the Exhibit button. You want to sign in as an administrative user to the Junos Pulse Access Control Service but are
unable to do so. You have verified that your username and password are correct.
Referring to the exhibit, what is causing this issue?
A. You are not signing in to the correct sign-in URL.
B. You are not authorized to sign in as an administrator.
C. You are not logging in to the device at the correct time of day.
D. You are not connecting to the authentication server.
正解:A


 718 お客様のコメント
718 お客様のコメント





川上** -
とても読みやすくて5日で読み終わることができました。そして早速試験に受けで、ほんとに合格できましたよ!嬉しいすぎます。