A university's help desk is receiving reports that Internet access on campus is not functioning. The network administrator looks at the management tools and sees the 1Gbps Internet is completely saturated with ingress traffic. The administrator sees the following output on the Internet router:
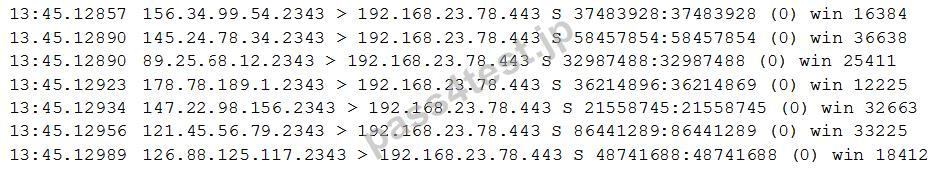
The administrator calls the university's ISP for assistance, but it takes more than four hours to speak to a network engineer who can resolve the problem. Based on the information above, which of the following should the ISP engineer do to resolve the issue?
A. A university web server is under increased load during enrollment. The ISP engineer should immediately increase bandwidth to 2Gbps to restore Internet connectivity. In the future, the university should pay for more bandwidth to handle spikes in web server traffic.
B. The ISP engineer should begin refusing network connections to the web server immediately to restore Internet connectivity on campus. The university should purchase an IPS device to stop DDoS attacks in the future.
C. The ISP engineer should immediately begin blocking IP addresses that are attacking the web server to restore Internet connectivity. In the future, the university should install a WAF to prevent this attack from happening again.
D. The ISP engineer should null route traffic to the web server immediately to restore Internet connectivity. The university should implement a remotely triggered black hole with the ISP to resolve this more quickly in the future.
正解:B
質問 2:
A secure facility has a server room that currently is controlled by a simple lock and key. and several administrators have copies of the key. To maintain regulatory compliance, a second lock, which is controlled by an application on the administrators' smartphones, is purchased and installed. The application has various authentication methods that can be used. The criteria for choosing the most appropriate method are:
* It cannot be invasive to the end user
* It must be utilized as a second factor.
* Information sharing must be avoided
* It must have a low false acceptance rate
Which of the following BEST meets the criteria?
A. Fingerprint scanning
B. Complex passcode
C. Facial recognition
D. Swipe pattern
E. Token card
正解:A
質問 3:
A company's Internet connection is commonly saturated during business hours, affecting Internet availability. The company requires all Internet traffic to be business related After analyzing the traffic over a period of a few hours, the security administrator observes the following:
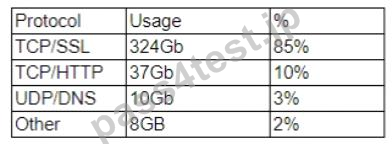
The majority of the IP addresses associated with the TCP/SSL traffic resolve to CDNs Which of the following should the administrator recommend for the CDN traffic to meet the corporate security requirements?
A. Implement an IPS to drop packets associated with the CDN.
B. Block outbound SSL traffic to prevent data exfiltration.
C. Further investigate the traffic using a sanctioned MITM proxy.
D. Confirm the use of the CDN by monitoring NetFlow data
正解:B
質問 4:
An organization is considering the use of a thin client architecture as it moves to a cloud-hosted environment. A security analyst is asked to provide thoughts on the security advantages of using thin clients and virtual workstations. Which of the following are security advantages of the use of this combination of thin clients and virtual workstations?
A. Malicious users will have reduced opportunities for data extractions from their physical thin client workstations, this reducing the effectiveness of local attacks.
B. Malicious insiders will not have the opportunity to tamper with data at rest and affect the integrity of the system.
C. Thin client workstations require much less security because they lack storage and peripherals that can be easily compromised, and the virtual workstations are protected in the cloud where security is outsourced.
D. All thin clients use TPM for core protection, and virtual workstations use vTPM for core protection with both equally ensuring a greater security advantage for a cloud-hosted environment.
正解:C
質問 5:
A product owner is working w*h a security engineer to improve the security surrounding certificate revocation which is important for the clients using a web application. The organization is currently using a CRL configuration to manage revocation, but it is looking for a solution that addresses the reporting delays associated with CRLs. The security engineer recommends OCSP but the product owner is concerned about the overhead associated with its use Which of the following would the security engineer MOST likely suggest to address the product owner's concerns?
A. The organization should use wildcard certificates
B. S/MIME can be used m lieu of OCSP
C. Key escrow can be used on the WAF
D. Stapling should be used with OCSP
正解:D
質問 6:
Given the following code snippet:
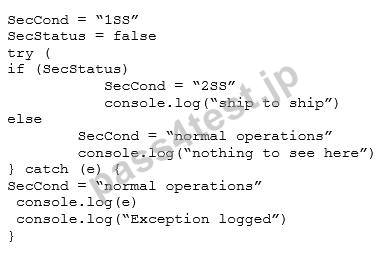
Which of the following failure modes would the code exhibit?
A. Halt
B. Exception
C. Secure
D. Open
正解:B


 667 お客様のコメント
667 お客様のコメント クリック」
クリック」





田中** -
Pass4Test様のCAS-003参考書問題集を利用して、見事合格しました。
問題は多数出題され、問題を解くスピードも速いです。ありがとうございました。