A security architect is reviewing the code for a company's financial website. The architect suggests adding the following HTML element, along with a server-side function, to generate a random number on the page used to initiate a funds transfer:
<input type="hidden" name="token" value=generateRandomNumber()>
Which of the following attacks is the security architect attempting to prevent?
A. XSRF
B. SQL injection
C. XSS
D. Clickjacking
正解:D
質問 2:
Company.org has requested a black-box security assessment be performed on key cyber terrain. On area of concern is the company's SMTP services. The security assessor wants to run reconnaissance before taking any additional action and wishes to determine which SMTP server is Internet-facing.
Which of the following commands should the assessor use to determine this information?
A. nc -v company.org
B. whois company.org
C. dnsrecon -d company.org -t SOA
D. dig company.org mx
正解:C
質問 3:
Given the following code snippet:
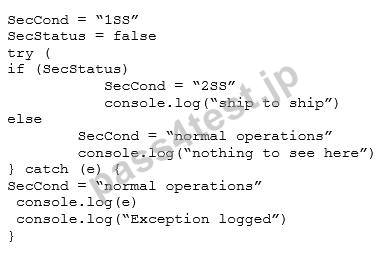
Which of the following failure modes would the code exhibit?
A. Halt
B. Exception
C. Secure
D. Open
正解:B
質問 4:
A company recently migrated to a SaaS-based email solution. The solution is configured as follows.
* Passwords are synced to the cloud to allow for SSO
* Cloud-based antivirus is enabled
* Cloud-based anti-spam is enabled
* Subscription-based blacklist is enabled
Although the above controls are enabled, the company's security administrator is unable to detect an account compromise caused by phishing attacks in a timely fashion because email logs are not immediately available to review. Which of the following would allow the company to gam additional visibility and reduce additional costs? (Select TWO)
A. Implement a third-party CASB solution.
B. Add email servers to NOC monitoring
C. Migrate the email antivirus and anti-spam on-premises
D. Install a virtual SIEM within the email cloud provider
E. Disable the current SSO model and enable federation
F. Feed the attacker IPs from the company IDS into the email blacklist
正解:A,D
質問 5:
The legal department has required that all traffic to and from a company's cloud-based word processing and email system is logged. To meet this requirement, the Chief Information Security Officer (CISO) has implemented a next-generation firewall to perform inspection of the secure traffic and has decided to use a cloud-based log aggregation solution for all traffic that is logged. Which of the following presents a long-term risk to user privacy in this scenario?
A. Confidential or sensitive documents are inspected by the firewall before being logged.
B. Latency when viewing videos and other online content may increase.
C. Reports generated from the firewall will take longer to produce due to more information from inspected traffic.
D. Stored logs may contain non-encrypted usernames and passwords for personal websites.
正解:A
質問 6:
A security analyst is trying to identify the source of a recent data loss incident. The analyst has reviewed all the for the time surrounding the identified all the assets on the network at the time of the data loss. The analyst suspects the key to finding the source was obfuscated in an application. Which of the following tools should the analyst use NEXT?
A. Log reduction and analysis tool
B. Software Decomplier
C. Static code analysis
D. Network enurrerator
正解:B


 1263 お客様のコメント
1263 お客様のコメント クリック」
クリック」





Matsumoto -
模擬テスト2週間ぐらいやって、合格できました。
時間的にもかなり余裕があって、ひとつひとつ解けました。
良い参考書でした。ありがとうございました。