Matt, the network engineer, has been tasked with separating network traffic between virtual machines on a single hypervisor. Which of the following would he implement to BEST address this requirement? (Select TWO).
A. NAT
B. System partitioning
C. VLAN
D. Disable spanning tree
E. Virtual switch
F. Access-list
正解:C,E
質問 2:
Joe, the security administrator, has determined that one of his web servers is under attack. Which of the following can help determine where the attack originated from?
A. Screenshots
B. Capture system image
C. Record time offset
D. Network sniffing
正解:D
質問 3:
A company has purchased an application that integrates into their enterprise user directory for account authentication. Users are still prompted to type in their usernames and passwords. Which of the following types of authentication is being utilized here?
A. Same sign-on
B. Single sign-on
C. Least privilege
D. Separation of duties
正解:A
質問 4:
DRAG DROP
Determine the types of Attacks from right to specific action.
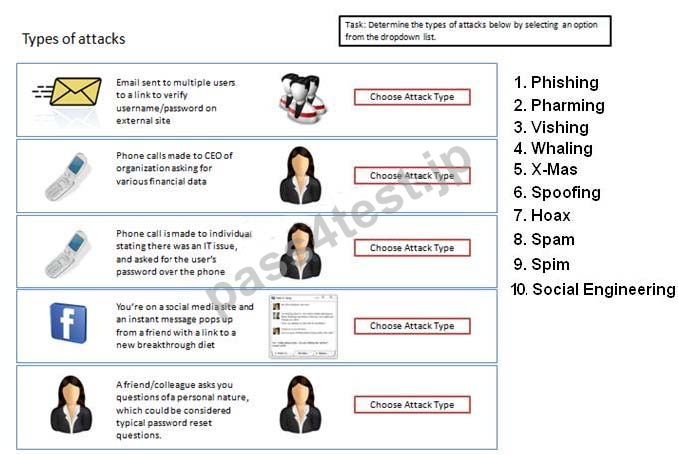
正解:
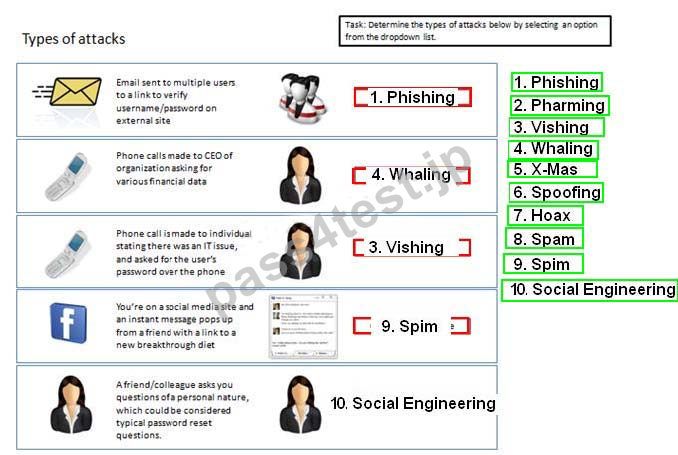
Explanation:
A) Phishing.
B) Whaling.
C) Vishing.
D) SpimE. Social engineering.
質問 5:
Which of the following is synonymous with a server's certificate?
A. Recovery agent
B. Public key
C. Private key
D. CRL
正解:B
質問 6:
Based on information leaked to industry websites, business management is concerned that unauthorized employees are accessing critical project information for a major, well-known new product. To identify any such users, the security administrator could:
A. Apply security updates and harden the OS on all project servers.
B. Increase antivirus coverage of the project servers.
C. Set up a honeypot and place false project documentation on an unsecure share.
D. Block access to the project documentation using a firewall.
正解:C


 871 お客様のコメント
871 お客様のコメント





上岛** -
ても読みやすく、
解りやすく解説しています。とにかくやる気が起こるSY0-301テキストです。