弊社のApplication Security問題集を利用すれば必ず試験に合格できます。
Pass4TestのECCouncil 312-96問題集はIT認定試験に関連する豊富な経験を持っているIT専門家によって研究された最新バージョンの試験参考書です。ECCouncil 312-96問題集は最新のECCouncil 312-96試験内容を含んでいてヒット率がとても高いです。Pass4TestのECCouncil 312-96問題集を真剣に勉強する限り、簡単に試験に合格することができます。弊社の問題集は100%の合格率を持っています。これは数え切れない受験者の皆さんに証明されたことです。100%一発合格!失敗一回なら、全額返金を約束します!
一年間無料で問題集をアップデートするサービスを提供します。
弊社の商品をご購入になったことがあるお客様に一年間の無料更新サービスを提供いたします。弊社は毎日問題集が更新されたかどうかを確認しますから、もし更新されたら、弊社は直ちに最新版の312-96問題集をお客様のメールアドレスに送信いたします。ですから、試験に関連する情報が変わったら、あなたがすぐに知ることができます。弊社はお客様がいつでも最新版のECCouncil 312-96学習教材を持っていることを保証します。
弊社の312-96問題集のメリット
Pass4Testの人気IT認定試験問題集は的中率が高くて、100%試験に合格できるように作成されたものです。Pass4Testの問題集はIT専門家が長年の経験を活かして最新のシラバスに従って研究し出した学習教材です。弊社の312-96問題集は100%の正確率を持っています。弊社の312-96問題集は多肢選択問題、単一選択問題、ドラッグ とドロップ問題及び穴埋め問題のいくつかの種類を提供しております。
Pass4Testは効率が良い受験法を教えてさしあげます。弊社の312-96問題集は精確に実際試験の範囲を絞ります。弊社の312-96問題集を利用すると、試験の準備をするときに時間をたくさん節約することができます。弊社の問題集によって、あなたは試験に関連する専門知識をよく習得し、自分の能力を高めることができます。それだけでなく、弊社の312-96問題集はあなたが312-96認定試験に一発合格できることを保証いたします。
行き届いたサービス、お客様の立場からの思いやり、高品質の学習教材を提供するのは弊社の目標です。 お客様がご購入の前に、無料で弊社の312-96試験「Certified Application Security Engineer (CASE) JAVA」のサンプルをダウンロードして試用することができます。PDF版とソフト版の両方がありますから、あなたに最大の便利を捧げます。それに、312-96試験問題は最新の試験情報に基づいて定期的にアップデートされています。

弊社は無料でApplication Security試験のDEMOを提供します。
Pass4Testの試験問題集はPDF版とソフト版があります。PDF版の312-96問題集は印刷されることができ、ソフト版の312-96問題集はどのパソコンでも使われることもできます。両方の問題集のデモを無料で提供し、ご購入の前に問題集をよく理解することができます。
簡単で便利な購入方法:ご購入を完了するためにわずか2つのステップが必要です。弊社は最速のスピードでお客様のメールボックスに製品をお送りします。あなたはただ電子メールの添付ファイルをダウンロードする必要があります。
領収書について:社名入りの領収書が必要な場合には、メールで社名に記入して頂き送信してください。弊社はPDF版の領収書を提供いたします。
ECCouncil Certified Application Security Engineer (CASE) JAVA 認定 312-96 試験問題:
1. Identify the type of attack depicted in the figure below:

A) Denial-of-Service attack
B) Cross-Site Request Forgery (CSRF) attack
C) SQL injection attack
D) XSS
2. The threat modeling phase where applications are decomposed and their entry points are reviewed from an attacker's perspective is known as ________
A) Impact Analysis
B) Threat Identification
C) Attack Surface Evaluation
D) Threat Classification
3. Oliver, a Server Administrator (Tomcat), has set configuration in web.xml file as shown in the following screenshot. What is he trying to achieve?

A) He wants to transfer the entire data over encrypted channel
B) He wants to transfer only Session cookies over encrypted channel
C) He wants to transfer only response parameter data over encrypted channel
D) He wants to transfer only request parameter data over encrypted channel
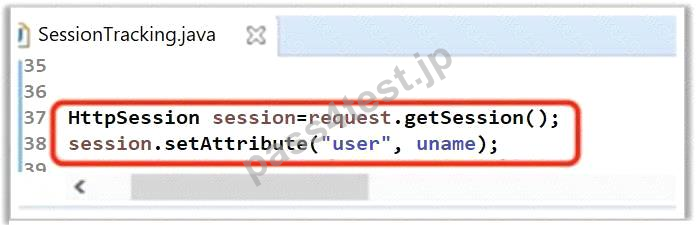
4. A developer has written the following line of code to handle and maintain session in the application. What did he do in the below scenario?
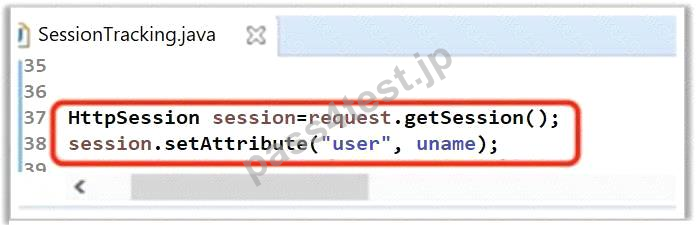
A) Maintained session by creating a Session variable user with value stored in uname variable.
B) Maintained session by creating a hidden variable user with value stored in uname variable.
C) Maintained session by creating a HTTP variable user with value stored in uname variable.
D) Maintained session by creating a Cookie user with value stored in uname variable.
5. Which line of the following example of Java Code can make application vulnerable to a session attack?

A) Line No. 5
B) Line No. 4
C) Line No. 1
D) Line No. 3
質問と回答:
質問 # 1
正解: D | 質問 # 2
正解: C | 質問 # 3
正解: A | 質問 # 4
正解: A | 質問 # 5
正解: D |


 746 お客様のコメント
746 お客様のコメント








栗田** -
必ず合格したい場合は細かな部分まで網羅してある問題集は312-96これが初めてかも!