Exhibit.
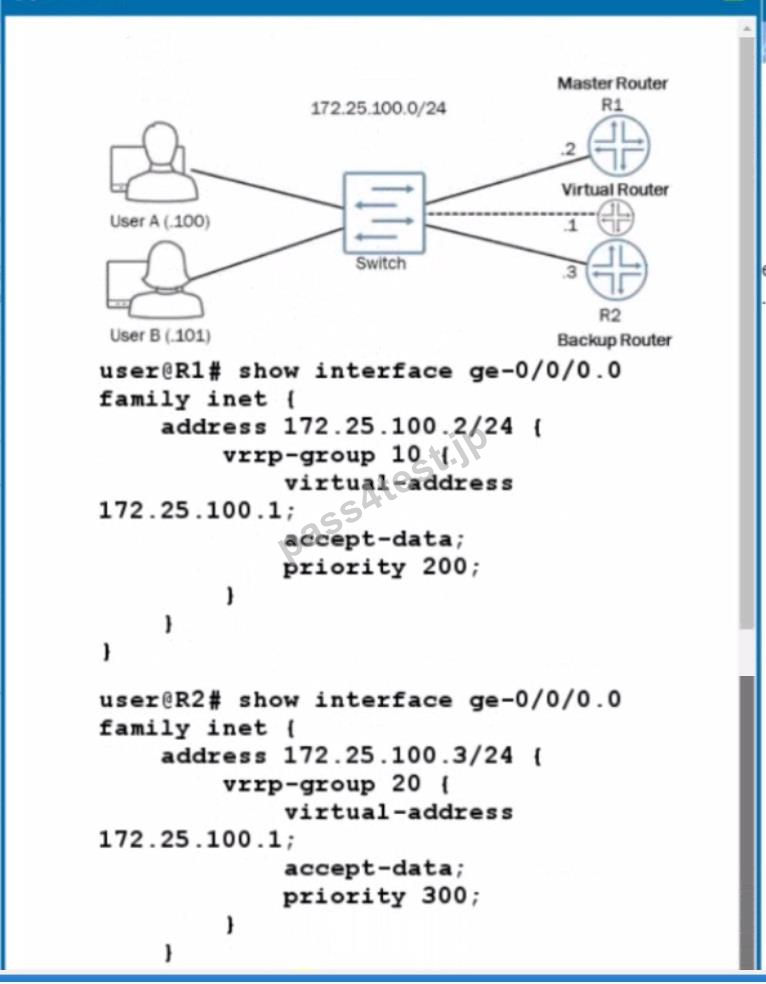
You are attempting to set up VRRP with R1 and R2 being participating members. You want R1 to be the master router and R2 to be the backup router with the virtual router they create being at address 172.25.100.1.
The virtual router is not pinging from either User A or User B.
Referring to the exhibit, what must be done to correct the problem?
A. A VRRP authentication type value is needed on R1 and R2.
B. A VRRP policy is needed on R1 and R2.
C. The VRRP group value on R1 and R2 must match.
D. The VRRP priority value on R1 and R2 must match
正解:C
質問 2:
You have configured the route with an IS-IS metric of 2048. However, the IS-IS interface metric of 63 is being applied for the interface of this router.
What must you do to enable larger metric value?
A. Enable level 1 IS-IS routing.
B. Enable wide metrics.
C. Restart the IS-IS protocol.
D. Disable narrow metrics.
正解:B
質問 3:
Exhibit.

Which statement is true about the configuration shown in the exhibit?
A. Only the add-community import policy will be evaluated routers are learned neighbor 172.30.1.1.
B. Both the add-community and local-pref import policies will be evaluated routes are learned from neighbor 172.30.2.1.
C. Only the local -pref import will be evaluated when routes are learned neighbor 172.301.1.
D. No import policy will be evaluated when routes are learned from neighbor 172.30.2.1.
正解:C
質問 4:
Exhibit.
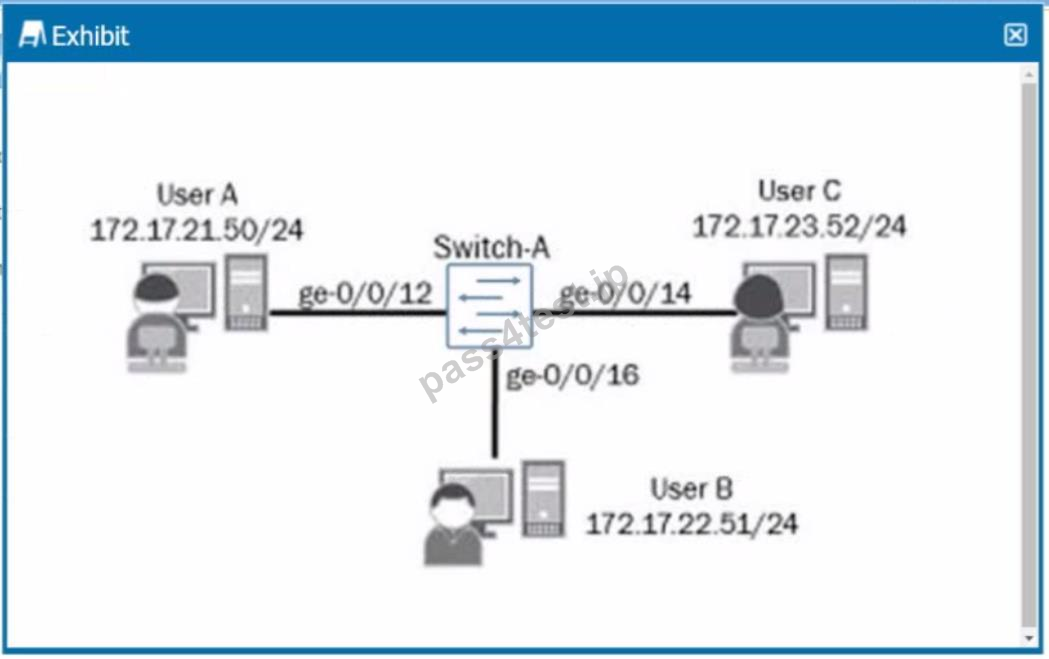
In the exhibit, each IP subnet in the network is associated with a unique VLAN ID.
Which action will ensure that Host C will communicate with Host A and Host B?
A. Configure all switch ports connecting to the host devices as trunk ports associated with all VLANs
B. Configure an IRB interface for each VLAN and associate It with its corresponding VLAN.
C. Configure a port-based ACL that permits inter-VLAN routing for all configured VLANs.
D. Configure all switch ports connecting to the host devices as access ports associated with a common VLAN.
正解:B
質問 5:
Which statement is correct about 13 IS link state PDUs?
A. They are used to build the link state database.
B. They are used to determine whether the neighbors are Level 1 or Level 2
C. They are used to maintain link slid.: database synchronization
D. They are used to establish adjacencies
正解:A
質問 6:
You have a conference room with an open network port that is used by employees to connect to the network.
You are concerned about rogue switches being connected to this port
Which two features should you enable on your switch to limit access to this port? (Choose two.)
A. dynamic ARP inspection
B. MAC limiting
C. DHCP snooping
D. 802.1X
正解:A,C


 766 お客様のコメント
766 お客様のコメント





冈田** -
きちんと問題集の内容を覚えました。
練習した問題がすべて出現しますので、すべて的中しました。とてもラッキだと思います。
やはり一番重要なのは暗記ですよね!