Which of the following traffic matches the authentication policy triggers authentication?
A. Access device or device initiated traffic
B. DHCP, BGP, OSPF and LDP packets
C. The first DNS packet corresponding to the HTTP service data flow
D. Traffic of visitors accessing HTTP services
正解:D
質問 2:
Which of the following is not a requirement for firewall double hot standby?
A. The firewall interface has the same IP address.
B. The firewall hardware model is consistent
C. The firewall software version is consistent
D. The type and number of the interface used are the same.
正解:A
質問 3:
In order to obtain evidence of crime, it is necessary to master the technology of intrusion tracking. Which of the following descriptions are correct about the tracking technology? (Multiple Choice)
A. Analysis of shallow mail behavior can analyze the information such as sending IP address, sending time, sending frequency, number of recipients, shallow email headers, etc.
B. Packet tagging technology extracts information from attack sources by recording packets on the router and then using data drilling techniques
C. Packet Recording Technology marks packets on each router that has been spoken by inserting trace data into the tracked IP packets.
D. Link detection technology determines the source of the attack by testing the network connection between the routers.
正解:A,C,D
質問 4:
Which of the following descriptions of the firewall fragment cache function are correct? (Multiple choice)
A. After the fragmented packet is directly forwarded, the firewall forwards the fragment according to the interzone security policy if it is not the fragmented packet of the first packet.
B. By default, the number of large fragment caches of an IPV4 packet is 32, and the number of large fragmentation buffers of an IPV6 packet is 255.
C. By default, the firewall caches fragmented packets.
D. For fragmented packets, NAT ALG does not support the processing of SIP fragmented packets.
正解:B,C,D
質問 5:
Which of the following statement is wrong about L2TP VPN?
A. Applicable to business employees dialing access to the intranet
B. Will not encrypt the data
C. Can be used in conjunction with IPsec VPN
D. Belongs to Layer 3 VPN technology
正解:D
質問 6:
Device destruction attacks are generally not easy to cause information leakage, but usually cause network communication services to be interrupted.
A. False
B. True
正解:B
質問 7:
ASPF (Application Specific Packet Filter) is a packet filtering technology based on the application layer, and implements a special security mechanism through the server-map table.
Which of the following statements about the ASPF and server-map tables are correct? (Multiple Choice)
A. The quintuple server-map entry implements a similar function to the session table.
B. ASPF dynamically allows multi-channel protocol data to pass through the server-map table.
C. ASPF monitors messages during communication
D. ASPF can dynamically create a server-map
正解:B,C,D
質問 8:
Through display ike sa to see the result as follows, which statements are correct? (Multiple choice)
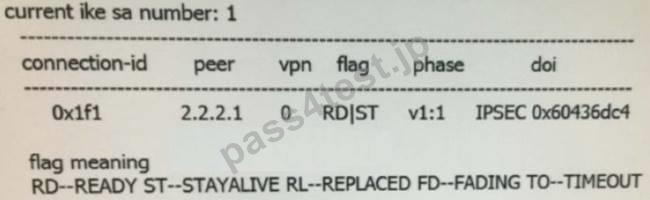
A. ike is using version v2
B. ike is using version v1
C. The second stage ipsec sa has been successfully established
D. The first stage ike sa has been successfully established
正解:B,D


 664 お客様のコメント
664 お客様のコメント





Hino -
身近なところから順番に学習できるようになっている点も良い点です。大判のテキストで問題も豊富。H12-711学習に良い