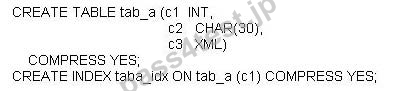
If table TAB_A and index TABA_IDX are created as follows:

What can be compressed?
A. All data in table TAB_
B. Only data in columns C1 and C2 of table TAB_A.
C. All data in table TAB_A and index TABA_IDX.
D. Only data in columns C1 and C2 in table TAB_A and index TABA_IDX.
正解:D
質問 2:
Which db2val option will create a log file?
A. -f
B. -r
C. -o
D. -l
正解:D
質問 3:
When using an SQL UPDATE statement on an XML column, which statement is valid?
A. An SQL UPDATE statement can modify a portion of an XML column using the SUBSTR function.
B. An SQL UPDATE statement cannot be used on an XML column.
C. An SQL UPDATE statement on an XML column must supply the complete new XML document.
D. An SQL UPDATE statement can update an XML column using an XMLQUERY transform expression.
正解:D
質問 4:
Which two registry variables that are normally used to delay or avoid acquiring locks are affected by Currently Committed (CC) semantics when the Cursor Stability (CS) isolation level are used? (Choose two.)
A. DB2_EVALUNCOMMITTED Extended Option:
B. DB2_EVALCOMMITTED Extended Option:
C. DB2_SKIPUPDATED Extended Option:
D. DB2_SKIPINSERTED Extended Option:
E. DB2_WAITFOROUTCOME Extended Option:
正解:A,D
質問 5:
Table TAB_A and index TABA_IDX were created by executing these SQL statements:
If this SQL statement is executed after 100,000 records have been inserted into table TAB_A:
ALTER INDEX taba_idx COMPRESS NO;
Which statement correctly describes what will happen to index TABA_IDX?
A. The index will remain compressed until it is REORGed.
B. The index will remain compressed until the COMPRESS attribute for table TAB_A has been set to NO and both the table and the index have been REORGed.
C. The index will remain compressed until the COMPRESS attribute for table TAB_A has been set to NO.
D. The index will be uncompressed immediately.
正解:A
質問 6:
Which function/stored procedure CANNOT be used to view audit facility data?
A. SYSPROC.AUDIT_ARCHIVE
B. SYSPROAUDIT_LIST_LOGS
C. SYSPROC.AUDIT_AUTH
D. SYSPROC.AUDIT_DELIM_EXTRACT
正解:C
質問 7:
The SALES database was created without AUTOMATIC STORAGE. If the following command is executed: ALTER DATABASE sales ADD STORAGE ON '/db2fs1', '/db2fs2' What is the expected result?
A. The SALES database and all its table spaces are converted to AUTOMATIC STORAGE.
B. The SALES database is converted to AUTOMATIC STORAGE, all new table spaces will use the AUTOMATIC STORAGE paths, existing table spaces need to be dropped and recreated.
C. The SALES database is converted to AUTOMATIC STORAGE, all new table spaces will use the AUTOMATIC STORAGE paths, ALTER TABLESPACE statement is needed to convert existing table spaces.
D. The SALES database is converted to AUTOMATIC STORAGE and all its existing DMS table spaces are in rebalance pending state.
正解:C
質問 8:
A DBA wants to use XQuery on a XML document to determine the number of lock waits for a particular workload. Which of the following table functions should be used?
A. MON_GET_WORKLOAD
B. MON_GET_LOCKS_DETAILS
C. MON_GET_WORKLOAD_DETAILS
D. MON_GET_LOCKS
正解:C





 0 お客様のコメント
0 お客様のコメント