A medium-sized company has recently launched an online product catalog. It has decided to keep the credit card purchasing in-house as a secondary potential income stream has been identified in relation to sales leads. The company has decided to undertake a PCI assessment in order to determine the amount of effort required to meet the business objectives. Which compliance category would this task be part of?
A. Government regulation
B. Company guideline
C. Industry standard
D. Company policy
正解:C
質問 2:
A network engineer wants to deploy user-based authentication across the company's wired and wireless infrastructure at layer 2 of the OSI model. Company policies require that users be centrally managed and authenticated and that each user's network access be controlled based on the user's role within the company. Additionally, the central authentication system must support hierarchical trust and the ability to natively authenticate mobile devices and workstations. Which of the following are needed to implement these requirements? (Select TWO).
A. PKI
B. WAYF
C. SAML
D. RADIUS
E. Shibboleth
F. LDAP
正解:D,F
解説: (Pass4Test メンバーにのみ表示されます)
質問 3:
An IT auditor is reviewing the data classification for a sensitive system. The company has classified the data stored in the sensitive system according to the following matrix:
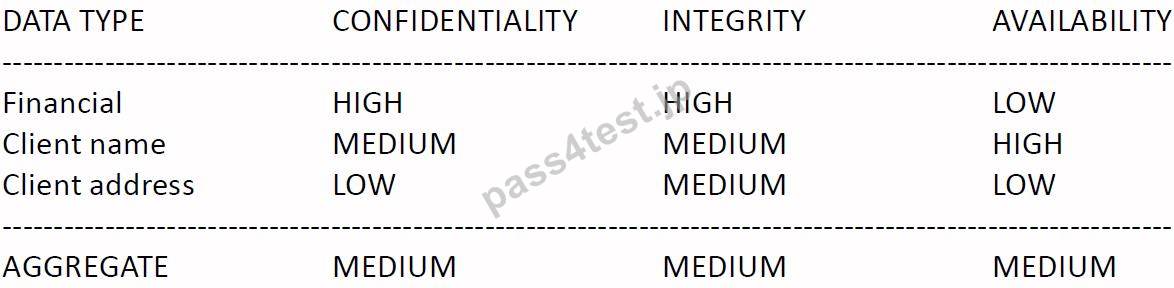
The auditor is advising the company to review the aggregate score and submit it to senior management.
Which of the following should be the revised aggregate score?
A. MEDIUM, MEDIUM, MEDIUM
B. HIGH, MEDIUM, LOW
C. MEDIUM, MEDIUM, LOW
D. HIGH, HIGH, HIGH
正解:D
解説: (Pass4Test メンバーにのみ表示されます)
質問 4:
A manager who was attending an all-day training session was overdue entering bonus and payroll information for subordinates. The manager felt the best way to get the changes entered while in training was to log into the payroll system, and then activate desktop sharing with a trusted subordinate. The manager granted the subordinate control of the desktop thereby giving the subordinate full access to the payroll system. The subordinate did not have authorization to be in the payroll system. Another employee reported the incident to the security team. Which of the following would be the MOST appropriate method for dealing with this issue going forward?
A. Block desktop sharing and web conferencing applications and enable use only with approval.
B. Actively monitor the data traffic for each employee using desktop sharing or web conferencing applications.
C. Permanently block desktop sharing and web conferencing applications and do not allow its use at the company.
D. Provide targeted security awareness training and impose termination for repeat violators.
正解:D
質問 5:
A security analyst has been asked to develop a quantitative risk analysis and risk assessment for the company's online shopping application. Based on heuristic information from the Security Operations
Center (SOC), a Denial of Service Attack (DoS) has been successfully executed 5 times a year. The
Business Operations department has determined the loss associated to each attack is $40,000. After implementing application caching, the number of DoS attacks was reduced to one time a year. The cost of the countermeasures was $100,000. Which of the following is the monetary value earned during the first year of operation?
A. $200,000
B. $100,000
C. $60,000
D. $140,000
正解:C
解説: (Pass4Test メンバーにのみ表示されます)


 819 お客様のコメント
819 お客様のコメント





南*歩 -
素敵です。無事試験にごうかくしました。万全の試験対策です。