Which of the following connectors uses the push-pull mechanism to make the connection?
Each correct answer represents a complete solution. Choose two.
A. LC
B. MT-RJ
C. SC
D. ST
正解:A,C
解説: (Pass4Test メンバーにのみ表示されます)
質問 2:
A computer user with an Internet connection and an opinion can post anything but there are some ethical and venerating behaviors that a user should consider before publishing contents on the Web.
Which of the following points should a user keep in mind before publishing any content on the Web?
Each correct answer represents a part of the solution. Choose all that apply.
A. Abstention from libelous statements
B. Respect for others
C. Respect for privacy
D. Factual Content
E. Effectual Content
正解:A,B,C,D
解説: (Pass4Test メンバーにのみ表示されます)
質問 3:
A computer network, often simply referred to as a network, is a collection of computers and devices connected by communications channels that facilitates communications among users. What are the benefits of a computer network? Each correct answer represents a complete solution. Choose all that apply.
A. Computers which are connected through a network can share resources as hard drives, printers, scanners, etc. with each other.
B. In a network environment, system maintenance can be performed from one central location.
C. A user can send files from one computer to another quite easily.
D. The functionality of all client computers on the network depend on the main server computer.
正解:A,B,C
解説: (Pass4Test メンバーにのみ表示されます)
質問 4:
Mark works as a Network Administrator for Company Inc. The company has a Windows-based network. The California branch of Company has been divided into two buildings in the same campus.
The company wants to interconnect these two buildings for proper communication among all the departments. Which of the following network types should Mark use to accomplish the task?
A. WAN
B. CAN
C. MAN
D. LAN
正解:B
解説: (Pass4Test メンバーにのみ表示されます)
質問 5:
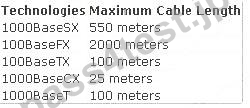
You are designing a TCP/IP-based network. You have to connect various offices in a premise. The major concern is to choose the appropriate technology that supports your requirement. Drag and drop the maximum cable lengths supported by their networking technologies to their respective boxes.
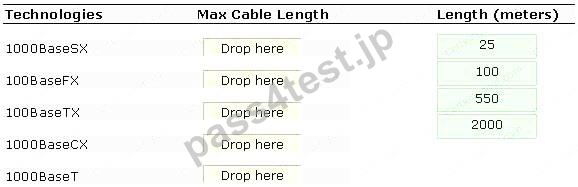
正解:
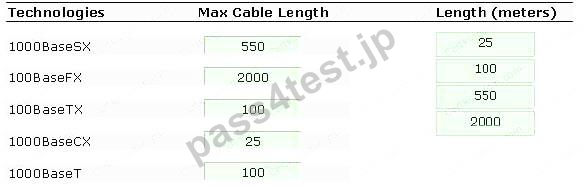
Explanation:
The maximum cable lengths supported by different technologies are shown in the table below:
質問 6:
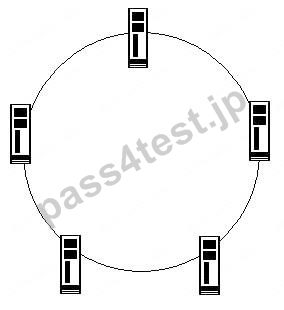
Mark the ring topology in the image below.
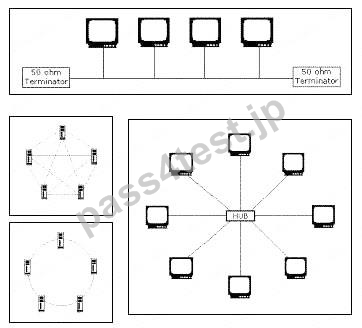
正解:
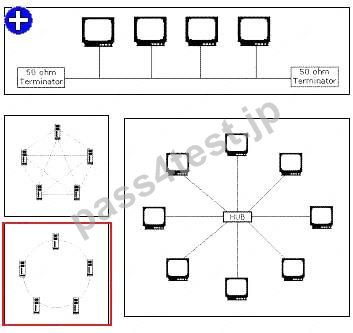
Explanation: Ring topology is a type of physical network design where all computers in the network are connected in a closed loop. Each computer or device in a Ring topology network acts as a repeater. It transmits data by passing a token around the network in order to prevent the collision of data between two computers that want to send messages at the same time. If a token is free, the computer waiting to send data takes it, attaches the data and destination address to the token, and sends it. When the token reaches its destination computer, the data is copied. Then, the token gets back to the originator. The originator finds that the message has been copied and received and removes the message from the token. Now, the token is free and can be used by the other computers in the network to send dat
A. In this topology, if one computer fails, the entire network
goes down.
Ring Topology:
質問 7:
Samantha works as a Web Developer for BlueWell Inc. She develops a Web application using Visual InterDev. She wants to group a series of HTML elements together so that an action can be performed collectively on them. Which of the following tags will Samantha use to accomplish this?
A. SPAN
B. DIV
C. BODY
D. GROUP
正解:B
解説: (Pass4Test メンバーにのみ表示されます)
質問 8:
Which of the following network cables is most vulnerable to Electromagnetic Interference (EMI) and Radio Frequency Interference (RFI)?
A. Fiber optic cable
B. Shielded Twisted Pair (STP)
C. Unshielded Twisted Pair (UTP)
D. Coaxial cable
正解:C
解説: (Pass4Test メンバーにのみ表示されます)
質問 9:
You work as a Security Administrator for Net Perfect Inc. The company has a Windows-based network. The employees use Internet Explorer for Internet surfing. You want to block access to the vulnerable sites from the internal network of the company. To accomplish the task, you need to configure some security settings for Internet Explorer. Which of the following features of Internet Explorer do you need to configure?
A. InPrivate Browsing
B. Pop-up blocker
C. Content Advisor
D. Internet Explorer Compatibility Evaluator
正解:C
解説: (Pass4Test メンバーにのみ表示されます)


 767 お客様のコメント
767 お客様のコメント





Ishihara -
これだけでも完璧に学習すれば、受かる可能性は大きい。IC3_GS4_LO勉強しやすい本だと思いました。