What module should an administrator use to view all activities in cloud applications?
A. Investigate
B. Protect
C. Audit
D. Detect
正解:B
質問 2:
Refer to the exhibit. What modules are used by the use case "Identify and determine business risk of cloud applications being used within the organization"?
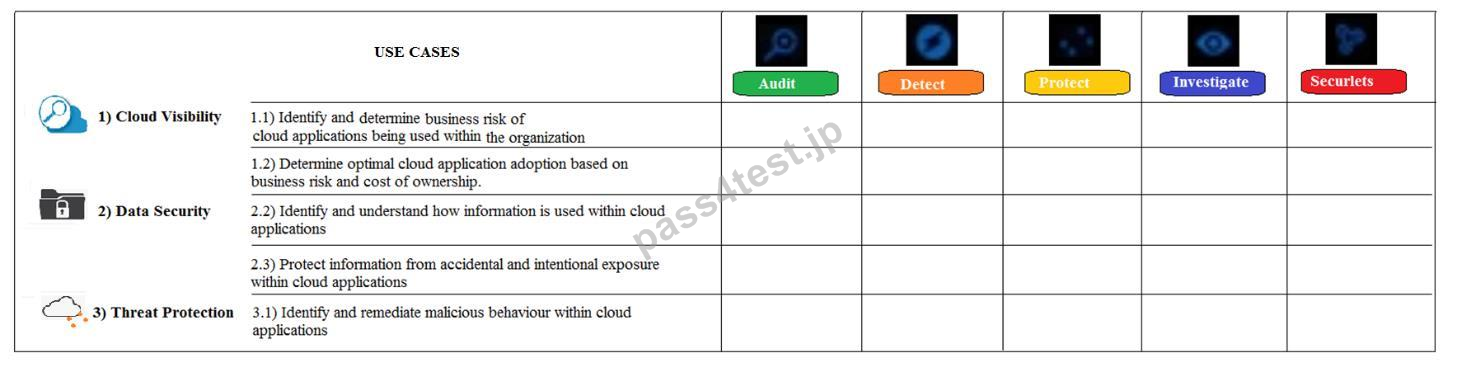
A. Investigate
B. Audit and Investigate
C. Audit
D. Audit and Securlets
正解:B
質問 3:
What type of policy should an administrator use to prevent a user that is behaving in anomalous ways from sharing public links while you monitor them?
A. File transfer
B. Access enforcement
C. Data exposure
D. Access monitoring
正解:B
質問 4:
What Rule Type in ContentIQ profiles do FERPA, GLBA, HIPAA, PCI AND PII belong to?
A. Keywords
B. Content types
C. Regular expressions
D. Risk types
正解:B
質問 5:
What compensatory control should an administrator implement if password quality rules of a cloud application has a low rating?
A. Biometric access
B. Role based access
C. Single Sign On (SSO)
D. Block the application
正解:C
質問 6:
Which CloudSOC module(s) use cloud application APIs as data sources?
A. Audit
B. Investigate and Securlets
C. Detect, Protect, Investigate, and Securlets
D. Detect, Protect, and Investigate
正解:B
質問 7:
Which are three (3) levels of data exposure?
A. Public, external, and internal
B. Public, semi-private, and private
C. Public, confidential, and company confidential
D. Public, confidential, and private
正解:A
質問 8:
What variable increases when a detector is triggered by a suspicious behavior?
A. ThreatScore
B. Risk Rating
C. Incident Index
D. Business Readiness Rating (BRR)
正解:A





 0 お客様のコメント
0 お客様のコメント