An administrator is configuring WebSphere Commerce Search using Advanced Configuration mode. Refer to the following image.
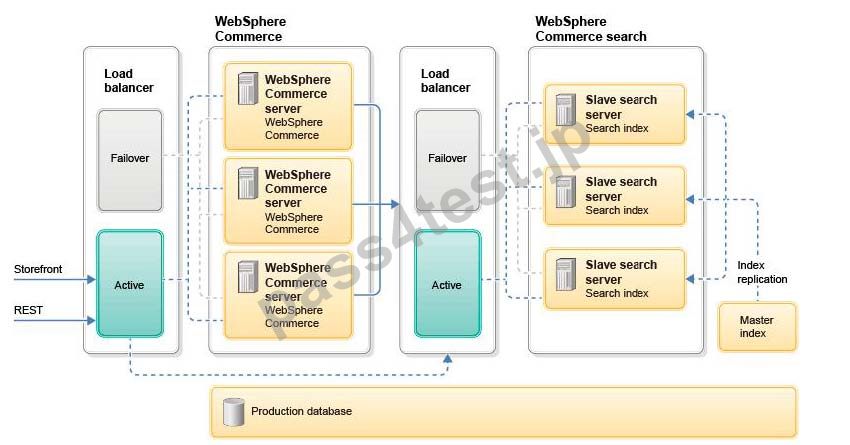
Which two of the following tasks must be performed to ensure that a proper deployment configuration exists in the production environment? (Select two.)
A. Configure Search administration requests to point to the Master index
B. Configure WebSphere Commerce to point to the search cluster for search requests
C. Expose the Master index externally
D. Always route live traffic to the primary node
E. Ensure that the replication configuration in the Master index points to each Slave search server
正解:B,E
質問 2:
An administrator is using the Configuration Manager client to reconfigure IBM WebSphere Commerce settings. Which action CANNOT be performed by this utility?
A. enable url-rewriting
B. modify ports that theadministration tools listen on
C. change the merchant key
D. enable application level security
正解:D
質問 3:
An administrator has been told that there are issues on some of the store pages, in which some of the page fragments appear more than once on the page. What is the cause of this issue and how can it be addressed?
A. This is caused by duplicate cache keys in the cache configuration. The administrator must double-check the cachepsec.xml file to ensure that all cache keys are unique.
B. This is caused by an invalid configuration, where the pages are full-page cached ("consume-subfragments"), but the fragments are set to "do-not-consume'Mhe administrator must turn off one of the two in order to avoid the issue.
C. This is caused by fragment-caching when the JSP does not have the necessary <%out.flush();%> statements around the include code for a subfragment. The administrator must direct the developer to add these statements and redeploy the application.
D. This is caused by cache corruption, an issue that sometimes occurs. The administrator should restart the nodes in the cluster.
正解:C
質問 4:
An administrator uses the Performance Measurement tool to generate the report-operationcache.csv performance report for operations.
Which metric within the report can then be used to measure whether the caching practices are inefficient or too efficient, and might be missing a key?
A. MAX_THEORIC_CACHE_HIT_PERCENTAGE
B. CACHE_EFFECTIVENESS_VS_THEORY_PERCENTAGE
C. CACHE_ENABLED_CALL_PERCENTAGE
D. MAX_CACHE_BENEFIT_MS
正解:B
質問 5:
If an administrator chooses to go with DMS tablespaces, in addition to re-defining the three user tablespaces, an additional 4K tablespace for index data will also need to be defined. The table definition in the schema creation file will need to be modified to point to the new tablespace.
Which file needs to be modified, if another additional tablespace is to be used for indexes?
A. <wcs install dir>/schema/db2/wcs.schema.sql
B. <wcs install dir>/schema/db2/wcs.tablespace.sql
C. <wcs install dir>/schema/db2/wcs.db2.sql
D. <wcs install dir>/schema/db2/wcs.index.sql
正解:B
質問 6:
A company created a new security policy to reduce the risk of data exposure. The new policy indicates that all the encrypted data stored in the enterprise must be re-encrypted on a regular basis.
How can this be accomplished in WebSphere Commerce V7.0 Feature Pack 8?
A. With the SHA-1 and SHA-2 algorithm provided by AES-128 and 3-DES, use the offline plug-in
B. Change the merchant key on a regular basis and use the migration tool provided in the product
C. Once the data is encrypted it cannot be changed in WebSphere Commerce
D. With the new NISTSP 800-131A and FIPS 140-2 security feature provided in FEP8, use the Key Locator Framework payment plug-in
正解:D


 870 お客様のコメント
870 お客様のコメント





Nakagawa -
この問題集だけでC8010-726認定資格を合格することができました。
勉強時間は一日一時間ぐらいで2週間ほどです。模擬試験を繰り返し勉強することはとても重要だと思います。
ご参考になれば幸いです。Pass4Test様もありがとうございました。