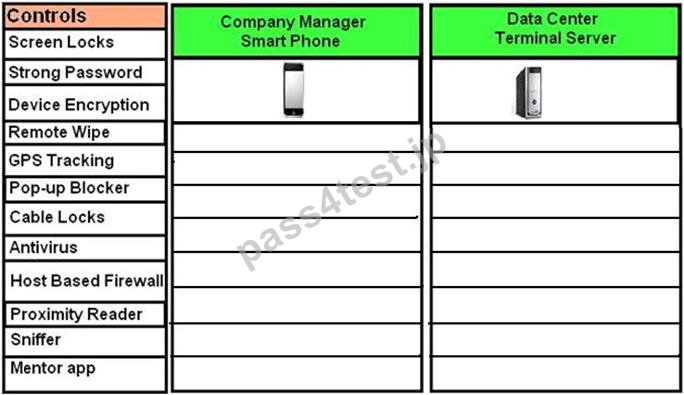
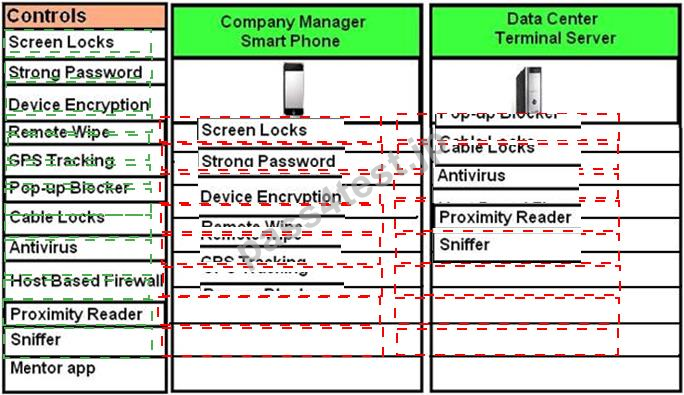
DRAG DROP
A Security administrator wants to implement strong security on the company smart phones and terminal servers located in the data center. Drag and Drop the applicable controls to each asset type.
Instructions: Controls can be used multiple times and not all placeholders needs to be filled. When you have completed the simul-ation, Please select Done to submit.
正解:
Explanation:
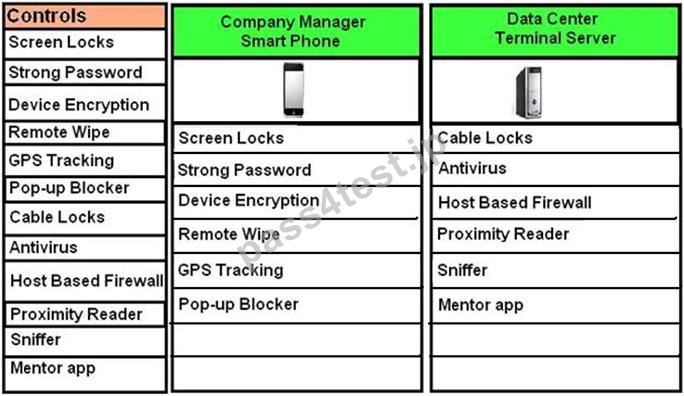
Cable locks are used as a hardware lock mechanism - thus best used on a Data Center Terminal Server.
Network monitors are also known as sniffers - thus best used on a Data Center Terminal Server.
Install antivirus software. Antivirus software should be installed and definitions kept current on all hosts. Antivirus software should run on the server as well as on every workstation. In addition to active monitoring of incoming fi les, scans should be conducted regularly to catch any infections that have slipped through- thus best used on a Data Center Terminal Server.
Proximity readers are used as part of physical barriers which makes it more appropriate to use on a center's entrance to protect the terminal server.
Mentor app is an Apple application used for personal development and is best used on a mobile device such as a smart phone.
Remote wipe is an application that can be used on devices that are stolen to keep data safe. It is basically a command to a phone that will remotely clear the data on that phone.
This process is known as a remote wipe, and it is intended to be used if the phone is stolen or going to another user.
Should a device be stolen, GPS (Global Positioning System) tracking can be used to identify its location and allow authorities to find it - thus best used on a smart phone.
Screen Lock is where the display should be configured to time out after a short period of inactivity and the screen locked with a password. To be able to access the system again, the user must provide the password. After a certain number of attempts, the user should not be allowed to attempt any additional logons; this is called lockout - thus best used on a smart phone.
Strong Password since passwords are always important, but even more so when you consider that the device could be stolen and in the possession of someone who has unlimited access and time to try various values - thus best use strong passwords on a smartphone as it can be stolen more easily than a terminal server in a data center.
Device Encryption- Data should be encrypted on the device so that if it does fall into the wrong hands, it cannot be accessed in a usable form without the correct passwords. It is recommended to you use Trusted Platform Module (TPM) for all mobile devices where possible.
Use pop-up blockers. Not only are pop-ups irritating, but they are also a security threat.
Pop-ups (including pop-unders) represent unwanted programs running on the system, and they can jeopardize the system's well-being. This will be more effective on a mobile device rather than a terminal server.
Use host-based firewalls. A firewall is the first line of defense against attackers and malware. Almost every current operating system includes a firewall, and most are turned on by Default- thus best used on a Data Center Terminal Server.
References:
Dulaney, Emmett and Chuck Eastton, CompTIA Security+ Study Guide, 6th Edition, Sybex, Indianapolis, 2014, pp. 221, 222, 369, 418
http://www.mentor-app.com/
質問 2:
A user is presented with the following items during the new-hire onboarding process:
-Laptop
-Secure USB drive
-Hardware OTP token
-External high-capacity HDD
-Password complexity policy
-Acceptable use policy
-HASP key
-Cable lock
Which of the following is one component of multifactor authentication?
A. Secure USB drive
B. HASP key
C. Hardware OTP token
D. Cable lock
正解:C
質問 3:
A company was recently audited by a third party. The audit revealed the company's network devices were transferring files in the clear. Which of the following protocols should the company use to transfer files?
A. HTTPS
B. SNMP3
C. LDAPS
D. SCP
正解:D
質問 4:
An organization is using a tool to perform a source code review. Which of the following describes the case in which the tool incorrectly identifies the vulnerability?
A. True negative
B. False positive
C. True positive
D. False negative
正解:B
質問 5:
DRAG DROP
You have been tasked with designing a security plan for your company. Drag and drop the appropriate security controls on the floor plan-Instructions: All objects must be used and all place holders must be filled. Order does not matter. When you have completed the simul- ation, please select the Done button to submit.
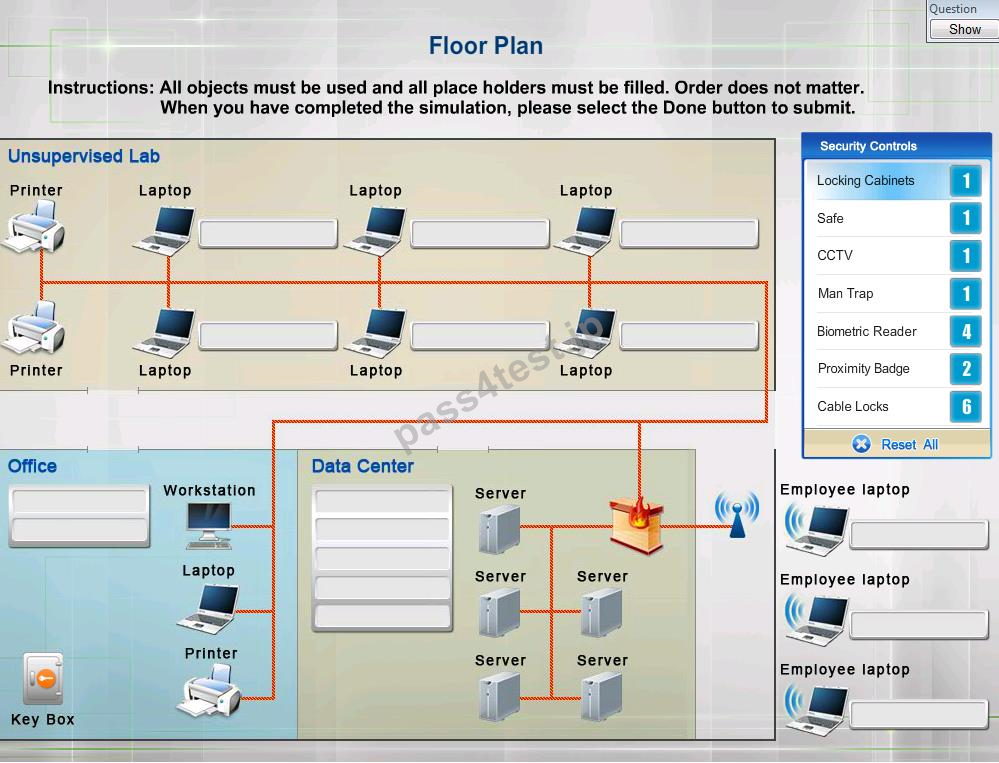
正解:
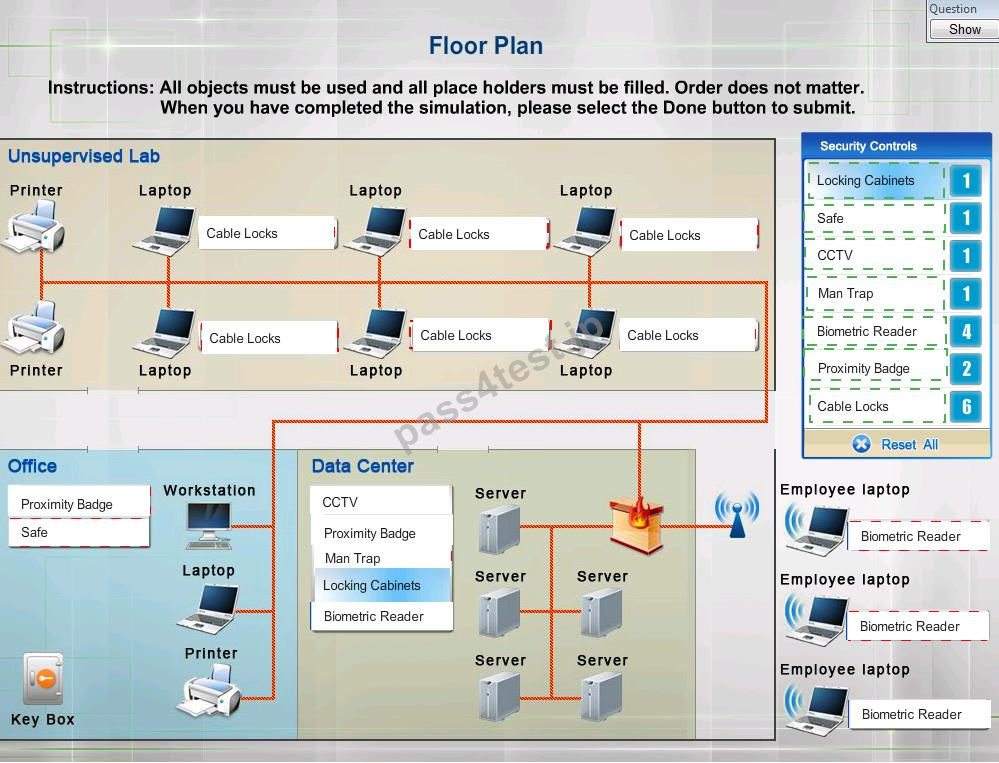
Explanation:
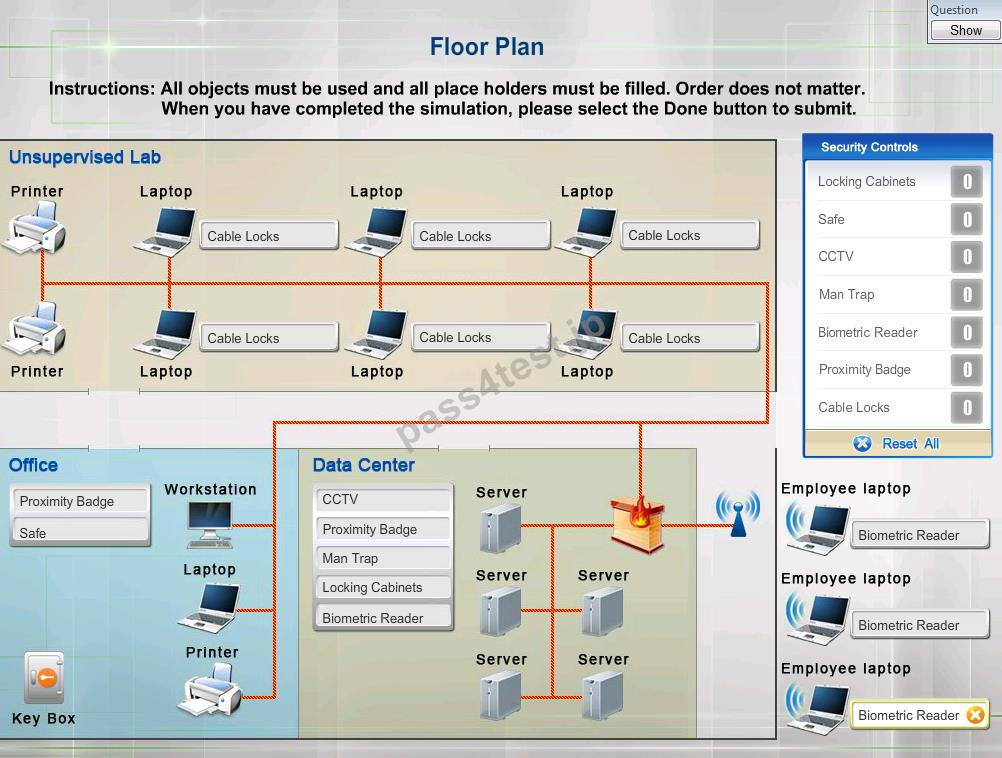
Cable locks - Adding a cable lock between a laptop and a desk prevents someone from picking it up and walking away Proximity badge + reader Safe is a hardware/physical security measure
Mantrap can be used to control access to sensitive areas.
CCTV can be used as video surveillance.
Biometric reader can be used to control and prevent unauthorized access.
Locking cabinets can be used to protect backup media, documentation and other physical artefacts.
References:
Dulaney, Emmett and Chuck Eastton, CompTIA Security+ Study Guide, 6th Edition, Sybex, Indianapolis, 2014, p. 369
質問 6:
DRAG DROP
A forensic analyst is asked to respond to an ongoing network attack on a server. Place the items in the list below in the correct order in which the forensic analyst should preserve them.
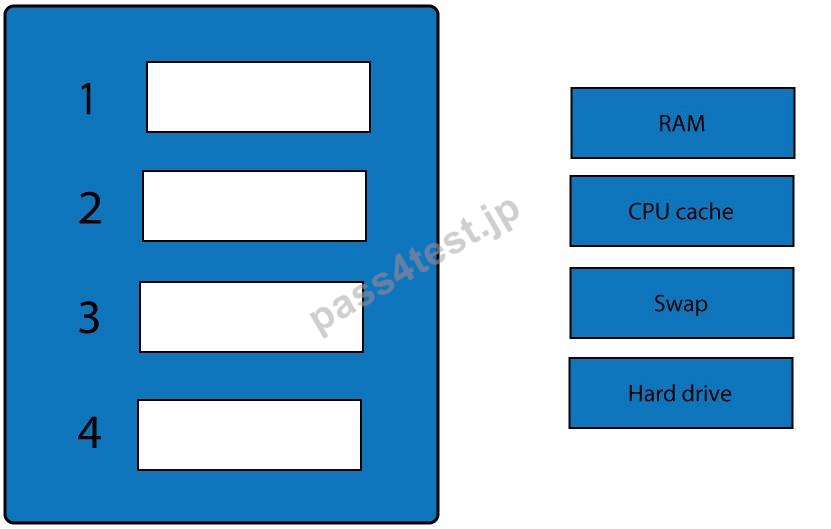
正解:
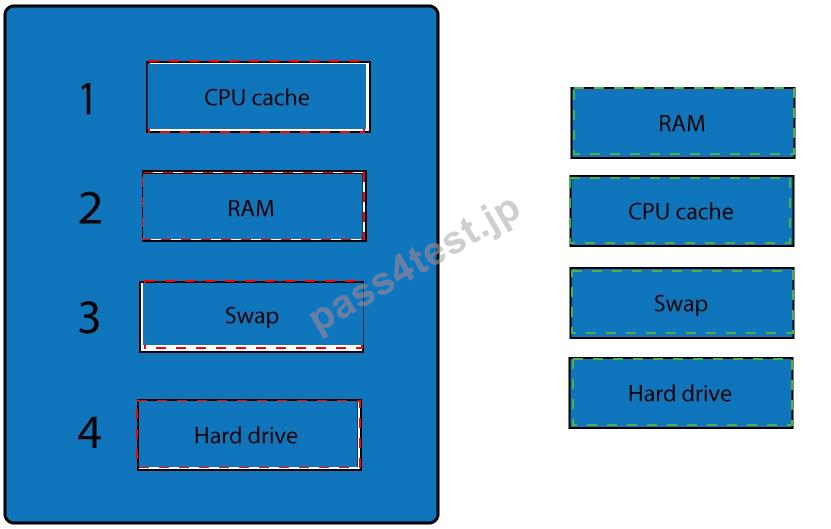
Explanation:
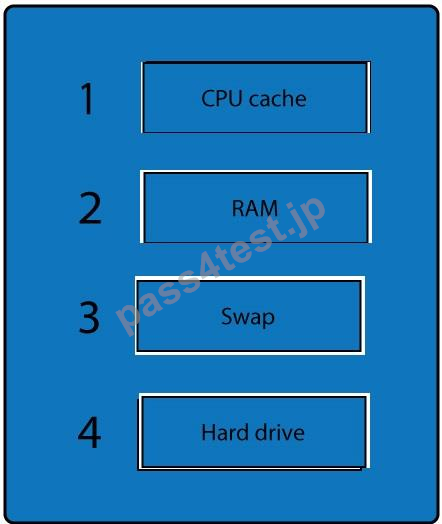
When dealing with multiple issues, address them in order of volatility (OOV); always deal with the most volatile first. Volatility can be thought of as the amount of time that you have to collect certain data before a window of opportunity is gone. Naturally, in an investigation you want to collect everything, but some data will exist longer than others, and you cannot possibly collect all of it once. As an example, the OOV in an investigation may be RAM, hard drive data, CDs/DVDs, and printouts.
Order of volatility: Capture system images as a snapshot of what exists, look at network traffic and logs, capture any relevant video/screenshots/hashes, record time offset on the systems, talk to witnesses, and track total man-hours and expenses associated with the investigation.
References:
Dulaney, Emmett and Chuck Eastton, CompTIA Security+ Study Guide, 6th Edition, Sybex, Indianapolis, 2014, p. 453
質問 7:
Joe, an employee, wants to show his colleagues how much he knows about smartphones.
Joe demonstrates a free movie application that he installed from a third party on his corporate smartphone. Joe's colleagues were unable to find the application in the app stores. Which of the following allowed Joe to install the application? (Select two.)
A. Rooting/jailbreaking
B. Near-field communication.
C. Tethering
D. Sideloading
E. Ad-hoc connections
正解:A,B
質問 8:
An administrator is replacing a wireless router. The configuration of the old wireless router was not documented before it stopped functioning. The equipment connecting to the wireless network uses older legacy equipment that was manufactured prior to the release of the 802.11i standard. Which of the following configuration options should the administrator select for the new wireless router?
A. WPA+CCMP
B. WPA2+CCMP
C. WPA2+TKIP
D. WPA+TKIP
正解:C


 869 お客様のコメント
869 お客様のコメント





长山** -
この問題集のすごいところは模擬問題だけを繰り返しても、百パーセント合格することができます。感謝しております。手軽に資格を取りたい方にも、ぜひオススメします。