Regarding ECA probe carrier entities, which of the following cannot be ECA probe carrier entities?
A. firewall
B. HiSec Insight flow probe
C. CE switch
D. S switch
正解:B
質問 2:
Which of the following options is used to obtain information in penetration testing? (single selection).
A. Connect to open ports Log in to the server
B. Use the tool to scan the port open by the server
C. Exploit the vulnerability to implant a backdoor into the host
D. Extract super administrator permissions for ordinary users.
正解:B
質問 3:
Which services in HUAWEI CLOUD solutions can data encryption be applied?
A. Database security
B. Vulnerability scanning service
C. Situational awareness services
D. Cloud host security
正解:A,D
質問 4:
In the Anh-DDos system What are the functions that ATIC can complete as a management center? (multiple selection).
A. Clean the flow
B. Report management
C. Policy discipline
D. reports an exception
正解:B,C
質問 5:
In * User Login Web Page with User Name and Password Medium The following is about Username" Which one is described correctly? (single selection).
A. Billing
B. Authorization
C. Identification
D. Identity authentication
正解:C
質問 6:
A description of the following IPv6 Secure Neighbor Discovery feature information for one of the interfaces Which one is wrong?
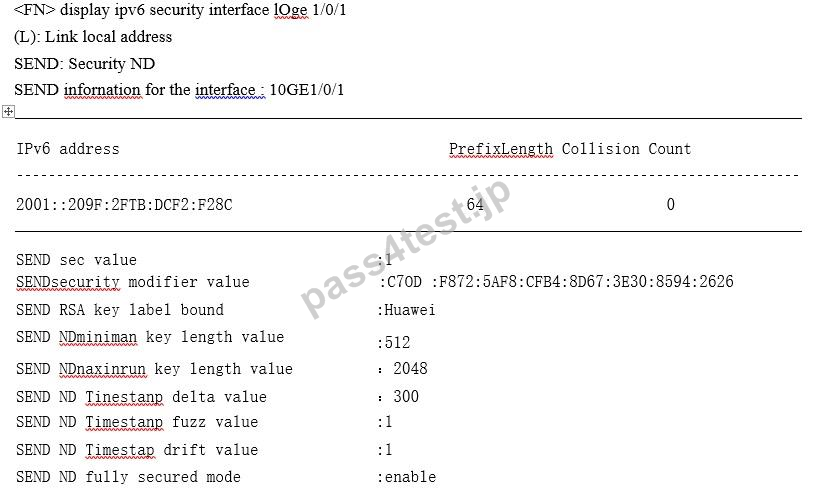
A. The interface does not have strict security mode enabled
B. The maximum key length that the interface can accept is 2048
C. The minimum key length that the interface can accept is 512
D. The security level of the CGA address is 1
正解:A
質問 7:
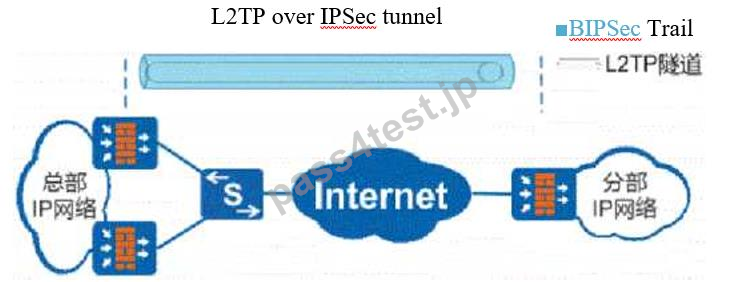
With the prevalence of e-commerce, online banking, e-government The business value of WEB servers is getting higher and higher, and the security threats faced by web servers are also increasing, and the defense against the web application layer has become an inevitable trend, WAF (WebApplication Firewall WEB APPLICATION FIREWALL) PRODUCTS BEGAN TO BECOME POPULAR. As shown in the figure The firewall uses the deployment mode of transparent proxy About the deployment mode of WAF using transparent proxy Which of the following options is described incorrectly.

A. You need to configure the IP address and route for the forwarding interface of the WAF
B. JUDGING FROM THE ANGULARITY OF THE WEB CLIENT THE WEB CLIENT IS STILL DIRECTLY ACCESSING THE SERVER AND IS NOT AWARE OF THE EXISTENCE OF WAF
C. The agent works in route-forwarding mode instead of bridge mode
D. Minimal network changes enable zero-configuration deployment
正解:A
質問 8:
Control of ping packets to the USG firewall itself The access control management function of the interface takes precedence over the security policy.
A. TRUE
B. FALSE
正解:A
質問 9:
Figure 1 shows the raw data table Figure 2 shows the data processed by K*anonymization technology, what is the K value of the processing? (Selection).
A. 4
B. 1
C. 3
D. 2
正解:A


 614 お客様のコメント
614 お客様のコメント





Tanami -
Pass4Testのおかげでいい参考書に出会えました。試験に挑んでみたいと思います。