Identify the correct properties of a partial mesh VPN deployment:
A. There are no hub locations in a partial mesh.
B. VPN tunnels are not configured between every single location.
C. Some locations are reached via a hub location.
D. VPN tunnels interconnect between every single location.
正解:B,C
質問 2:
Which of the following tasks fall under the responsibility of the SSL proxy in a typical HTTPS connection? (Select all that apply.)
A. The web server SSL handshake.
B. The web client SSL handshake.
C. File buffering.
D. Communication with the urlfilter process.
正解:A,B
質問 3:
Examine the following log message for IPS and identify the valid responses below. (Select all that apply.)
2012-07-01 09:54:28 oid=2 log_id=18433 type=ips subtype=anomaly pri=alert vd=root severity="critical" src="192.168.3.168" dst="192.168.3.170" src_int="port2" serial=0 status="detected" proto=1 service="icmp" count=1 attack_name="icmp_flood" icmp_id="0xa8a4" icmp_type="0x08" icmp_code="0x00" attack_id=16777316 sensor="1" ref="http://www.fortinet.com/ids/VID16777316" msg="anomaly: icmp_flood, 51 > threshold 50"
A. The target is 192.168.3.170.
B. The target is 192.168.3.168.
C. The attack was detected only.
D. The attack was detected and blocked.
E. The attack was TCP based.
正解:A,C
質問 4:
With FSSO, a domain user could authenticate either against the domain controller running the Collector Agent and Domain Controller Agent, or a domain controller running only the Domain Controller Agent.
If you attempt to authenticate with the Secondary Domain Controller running only the Domain Controller Agent, which of the following statements are correct? (Select all that apply.)
A. The FortiGate unit receives the user information from the Domain Controller Agent of the Secondary Controller.
B. The login event is sent to the Collector Agent.
C. The user cannot be authenticated with the FortiGate device in this manner because each Domain Controller Agent requires a dedicated Collector Agent.
D. The Collector Agent performs the DNS lookup for the authenticated client's IP address.
正解:B,D
質問 5:
Which of the following statements are correct about the HA diag command diagnose sys ha reset-uptime? (Select all that apply.)
A. The device this command is executed on is likely to switch from master to slave status if master override is enabled.
B. The device this command is executed on is likely to switch from master to slave status if master override is disabled.
C. This command resets the uptime variable used in the HA algorithm so it may cause a new master to become elected.
D. This command has no impact on the HA algorithm.
正解:B,C
質問 6:
Bob wants to send Alice a file that is encrypted using public key cryptography.
Which of the following statements is correct regarding the use of public key cryptography in this scenario?
A. Bob will use Alice's public key to encrypt the file and Alice will use Bob's public key to decrypt the file.
B. Bob will use his public key to encrypt the file and Alice will use Bob's private key to decrypt the file.
C. Bob will use Alice's public key to encrypt the file and Alice will use her private key to decrypt the file.
D. Bob will use his private key to encrypt the file and Alice will use her private key to decrypt the file.
E. Bob will use his public key to encrypt the file and Alice will use her private key to decrypt the file.
正解:C
質問 7:
When viewing the Banned User monitor in Web Config, the administrator notes the entry illustrated in the exhibit.
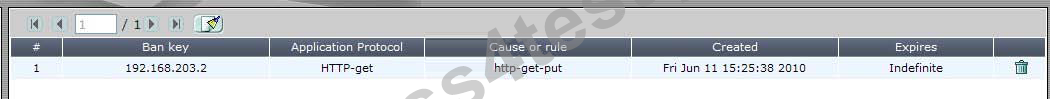
Which of the following statements is correct regarding this entry?
A. The entry displays a ban that has been added as a result of traffic triggering a configured DLP rule.
B. The entry displays a ban that was triggered by HTTP traffic matching an IPS signature. This client is banned from receiving or sending any traffic through the FortiGate.
C. This entry displays a ban entry that was added manually by the administrator on June11th.
D. The entry displays a quarantine, which could have been added by either IPS or DLP.
正解:A
質問 8:
Which of the following is an advantage of using SNMP v3 instead of SNMP v1/v2 when querying the FortiGate unit?
A. MIB-based report uploads
B. Packet encryption
C. SNMP access limits through access lists
D. Running SNMP service on a non-standard port is possible
正解:B


 714 お客様のコメント
714 お客様のコメント クリック」
クリック」





Hirano -
FCNSP.v5自学者向けの教科書だと思います。Pass4Testさん本当にありがとうございます。