In which step Steganography fits in CEH System Hacking Cycle (SHC)
A. Step 2: Crack the password
B. Step 5: Hide files
C. Step 6: Cover your tracks
D. Step 3: Escalate privileges
E. Step 4: Execute applications
F. Step 1: Enumerate users
正解:B
質問 2:
Jason is the network administrator of Spears Technology. He has enabled SNORT IDS to detect attacks going through his network. He receives Snort SMS alerts on his iPhone whenever there is an attempted intrusion to his network.
He receives the following SMS message during the weekend.
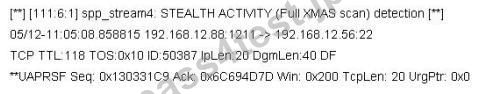
An attacker Chew Siew sitting in Beijing, China had just launched a remote scan on Jason's network with the hping command.
Which of the following hping2 command is responsible for the above snort alert?
A. chenrocks:/home/siew # hping -F -Q -J -A -C -W 192.168.2.56 -p 22 -c 5 -t 118
B. chenrocks:/home/siew # hping -D -V -R -S -Z -Y 192.168.2.56 -p 22 -c 5 -t 118
C. chenrocks:/home/siew # hping -S -R -P -A -F -U 192.168.2.56 -p 22 -c 5 -t 118
D. chenrocks:/home/siew # hping -G -T -H -S -L -W 192.168.2.56 -p 22 -c 5 -t 118
正解:C
質問 3:
What type of OS fingerprinting technique sends specially crafted packets to the remote OS and analyzes the received response?
A. Distributive
B. Active
C. Passive
D. Reflective
正解:B
質問 4:
You are trying to hijack a telnet session from a victim machine with IP address 10.0.0.5 to Cisco router at 10.0.0.1. You sniff the traffic and attempt to predict the sequence and acknowledgement numbers to successfully hijack the telnet session.
Here is the captured data in tcpdump.
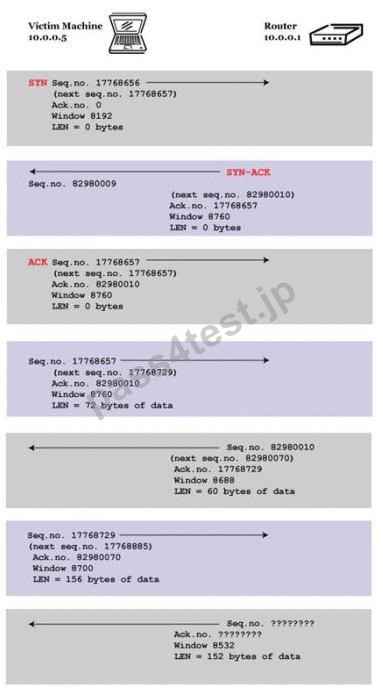
What are the next sequence and acknowledgement numbers that the router will send to the victim machine?
A. Sequence number: 82980010 Acknowledgement number: 17768885D.
B. Sequence number: 82980070 Acknowledgement number: 17768885A.
C. Sequence number: 17768729 Acknowledgement number: 82980070B.
D. Sequence number: 87000070 Acknowledgement number: 85320085C.
正解:B
質問 5:
What statement is true regarding LM hashes?
A. LM hashes are not generated when the password length exceeds 15 characters.
B. Uppercase characters in the password are converted to lowercase.
C. LM hashes are based on AES128 cryptographic standard.
D. LM hashes consist in 48 hexadecimal characters.
正解:A
質問 6:
You establish a new Web browser connection to Google. Since a 3-way handshake is required for any TCP connection, the following actions will take place.
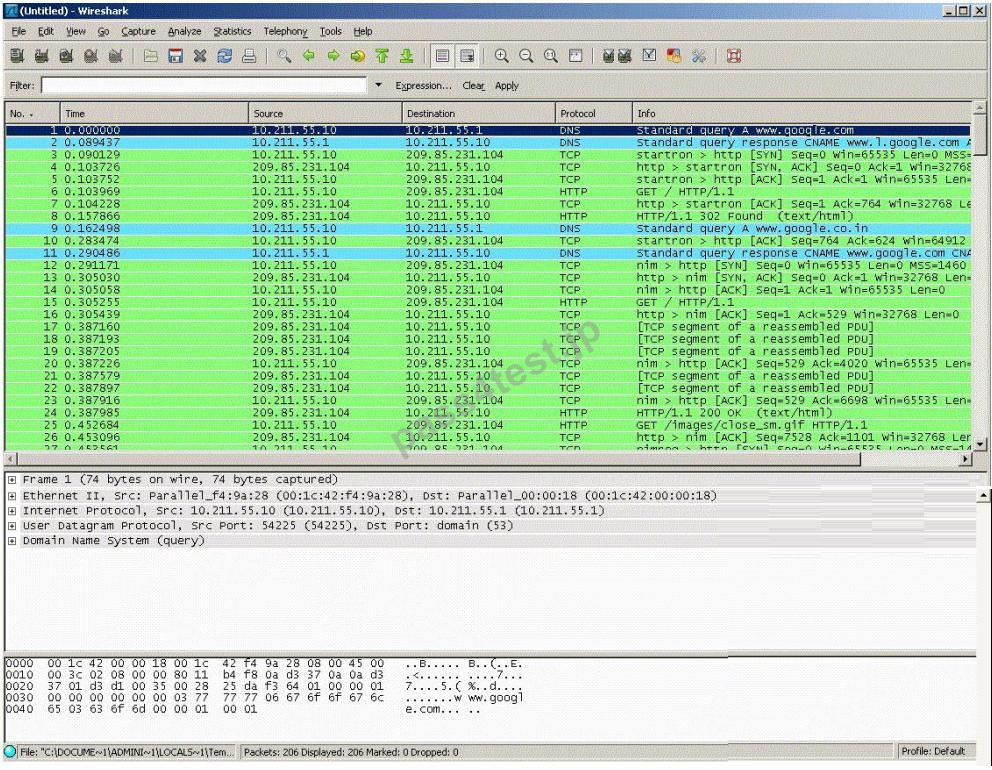
DNS query is sent to the DNS server to resolve www.google.com
DNS server replies with the IP address for Google?
SYN packet is sent to Google.
Google sends back a SYN/ACK packet
Your computer completes the handshake by sending an ACK
The connection is established and the transfer of data commences
Which of the following packets represent completion of the 3-way handshake?
A. 6th packet
B. 5th packet
C. 3rdpacket
D. 4th packet
正解:B


 613 お客様のコメント
613 お客様のコメント





Amakawa -
今日受験して、無事合格しました。
予測問題が大幅に的中されました。本当に感謝です。
問題や擬似問題集と回答などもあり、EC0-3501冊で試験に対応できる良い本だと思います。